
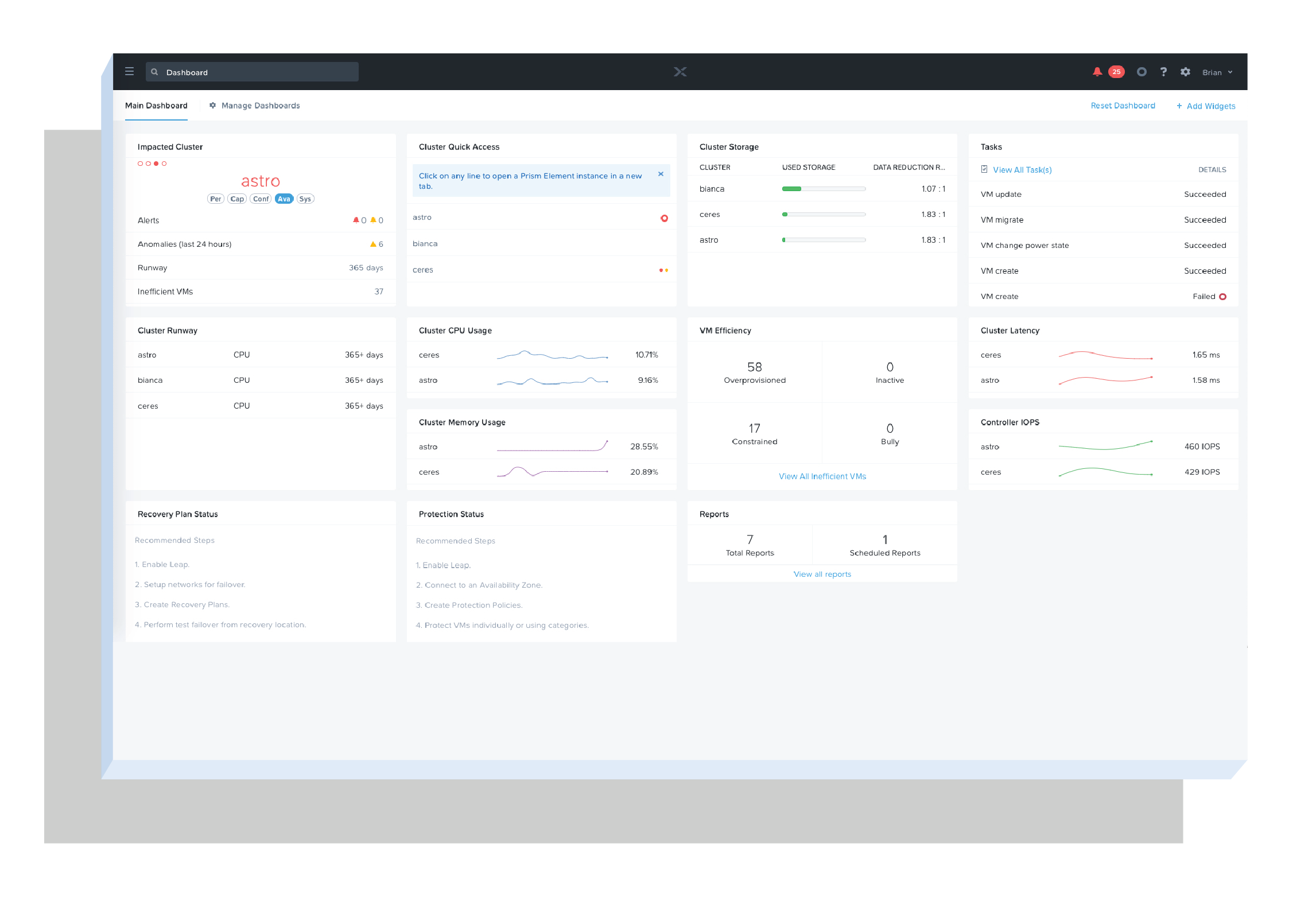
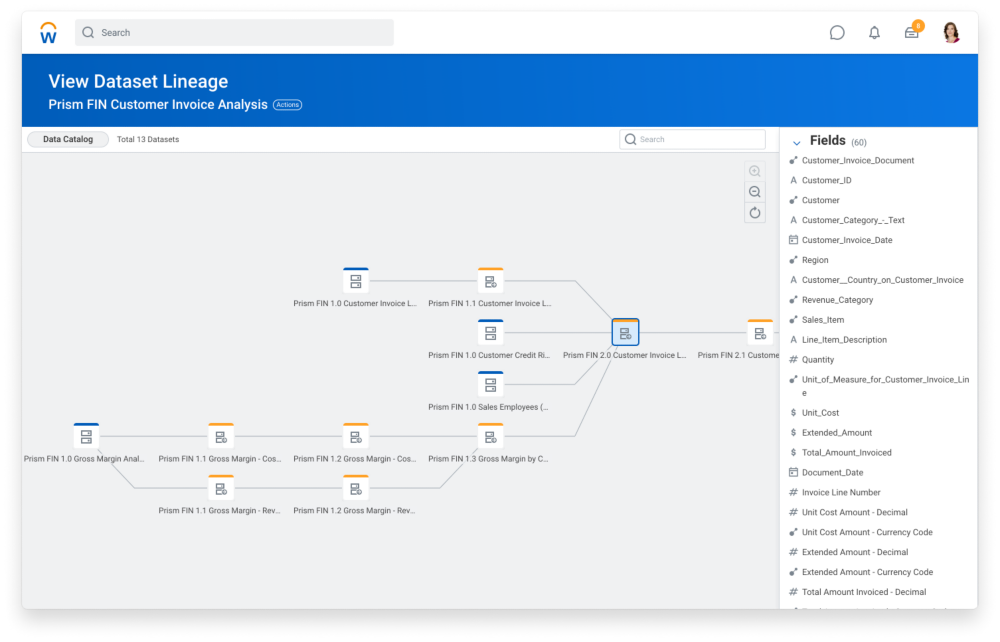
Manage Your Blue Prism Process by using Blue Prism Plugin with Workload Automation - WORKLOAD AUTOMATION COMMUNITY
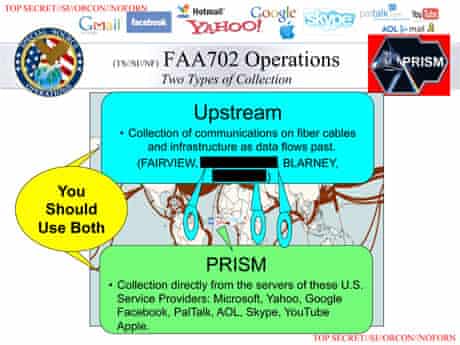
NSA's Prism surveillance program: how it works and what it can do | US national security | The Guardian

NSA Prism program taps in to user data of Apple, Google and others | US national security | The Guardian

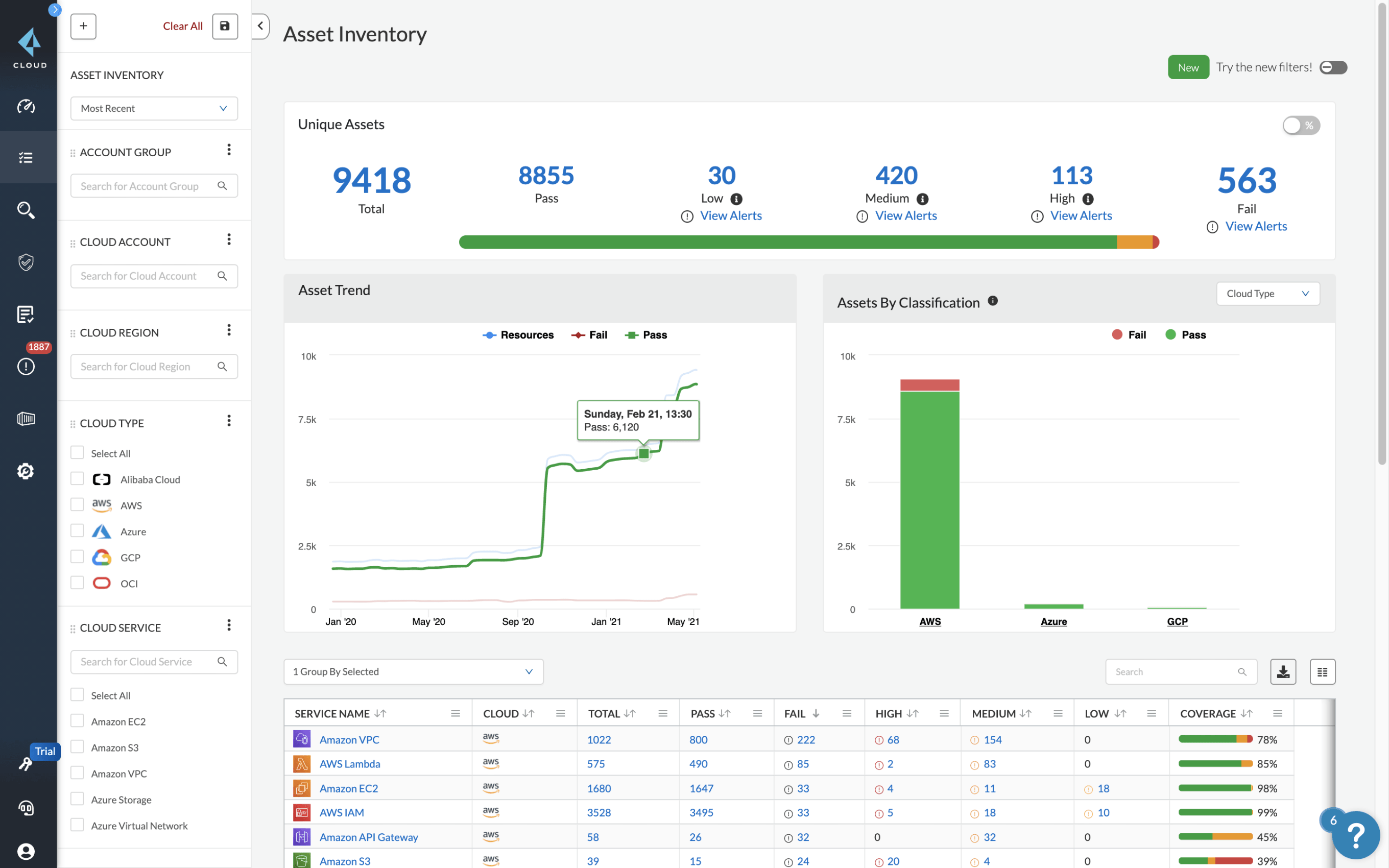
PRISM-AP: automated Wireless RogueAP MITM attack framework – Cyber Security | Security application, Cyber security, Technology world











![PDF] Impact of NSA-PRISM to National Information Security Strategy & Policy | Semantic Scholar PDF] Impact of NSA-PRISM to National Information Security Strategy & Policy | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/3667b3f7aec8bdcf8b741c1dca43139c8f48de54/4-Figure2-2.png)
